Last week I wrote about how to create a self-signed SSL certificate for your website. It turned out to be one of my popular posts, and the process turned out to be remarkably easy: you run one single command, make a quick change to your webserver configuration and you’re done.
Our self-signed certificate worked great for encrypting the connection between our browser and the webserver, but as I mentioned that’s only half the SSL story. Our certificate wasn’t trusted by our operating system, which means it couldn’t be used by our browser to confirm the identity of the server we’d connected to, which in turns means that visitors to our website are greeted with a big, bold “your connection is not secure” error message.
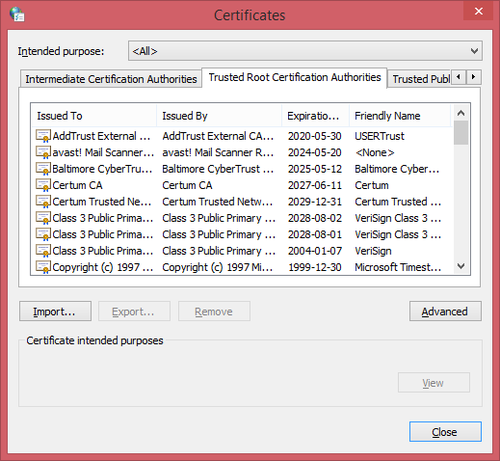
Our browser knows whether or not it can trust a given SSL certificate through a hierarchical structure. I’m glossing over some details, but essentially our operating system comes with a listed of trusted “root” certificates. The owners of these root certificates can produce certificates for their customers much as I produced one for myself last week. The difference is that there’s a mechanism for traceability here – the certificates they produce are trusted, because our browser can trace things back to the root certificate that it already knows to be good.
I’m not suggesting there’s some kind of conspiracy at play here, but it seems to me the owners of these root certificates have a metaphorical license to print money. They can create something out of nothing with, in essence, a single command, and sell it for a value they determine. I might be OK with that if they hadn’t determined that the value is so insanely high.
Luckily for us there are market forces at play in this whole story, and we don’t have to pony up the $1,500 Symantec are asking to secure our website traffic. We’re going to do it for free. Read on!
SSL Certificates and Their Value
Unfortunately, budget-minded certificate providers are few and far between, and the trend appears to be that their either disappearing or eliminating their lowest-cost options in favour of “better,” higher-priced ones. NameCheap is a good option if you’re looking to minimize costs, with certificates starting at around $10 at the time of writing.
But here’s the question: If you can get an SSL certificate from them for $10, why are Symantec charging $1,500. Is their option 150x better?
Here’s my answer: No.
Symantec would likely argue that point though, as you might imagine. They’d mention that they put their customers through a more stringent identification process in order to provide an increased level of confidence in their product. They know their customers, and they know they’re only issuing certificates to trustworthy sites. They’d argue they provide a warranty with their certificates that provides their customers with legal protection against a losses caused by a security breach.
This is all well and good, of course, but does the typical internet user care? I’d propose that the average site visitor – at best – notices the green padlock icon in the address bar and proceeds with confidence upon seeing it. How much you, as a site owner, pay to get that padlock icon really makes no difference to the vast majority of your visitors.
That all being said, it of course depends on what your site does. If you’re a bank, this is not an area you should be trying to save money in. Take the expensive certificate with the warranty and the legal protection. If you run an e-commerce site and your livelihood depends on your website then maybe don’t spend $1,500, but don’t accept the reputational risk of using a product with no warranty and limited support. If you’re me, though? Whatever, just spend as little money as possible.
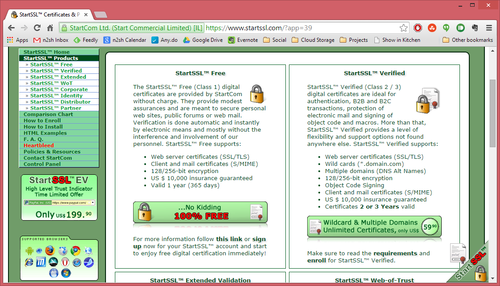
Getting a Free SSL Certificate
Enter our new best friends at StartSSL. They offer single-site SSL certificates for the extremely reasonable price of free. There are some caveats as you might expect, but none of them are a show-stopper for my purposes. Nevertheless the biggest thing you should consider is that although they’ll issue the certificate for free, you will have to pay if you ever need to revoke it. If you ever suffer a security breach and suspect that your certificate file has fallen into the wrong hands (I’m talking about the equivalent of the server.pem file we created for ourselves last week), it should be revoked to prevent some nefarious person setting up a site that masquerades as yours. If there’s ever another vulnerability similar to the heartbleed bug then the certificate should likewise be revoked.
In a nutshell, this is a risk tolerance question. By taking the free certificate you’re betting that nothing bad will happen during the 12-month life of your certificate or that if it does you’ll be prepared to accept a whole host of new risks.
Since I was OK with the many drawbacks of using a self-signed certificate, I laugh in the face of risks like the ones mentioned above. If you’re different then do your homework and make sure you’re getting a product that’s right for you, but if you’re like me then tune in next week when I walk through the steps of getting a free certificate issued to me and install it on my server.